Banks must add layered defenses against deepfakes

ENISA, NIST and FCA guidance and enforcement show synthetic media can bypass camera‑only liveness; banks need injection‑attack detection, device attestation and issuer‑signed credentials.
Regulatory guidance and enforcement actions warn that deepfakes can defeat camera‑only liveness checks and that banks must expand identity verification controls. ENISA, NIST and UK financial supervisors have separated capture‑device attacks from pipeline or software attacks and set expectations for broader evidence at onboarding.
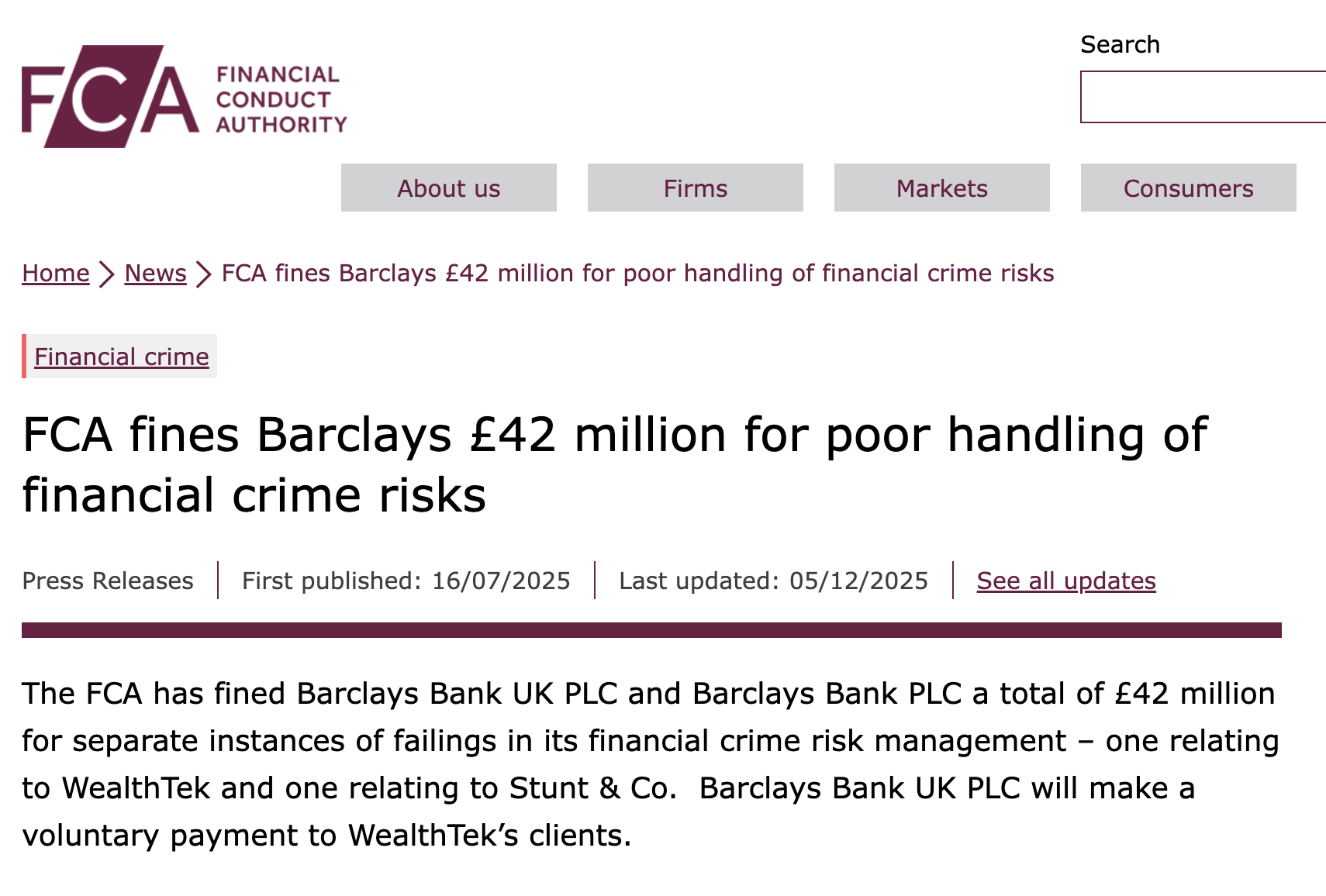
Fraud reporting and enforcement figures underline the trend. Cifas recorded about 250,000 identity‑fraud filings in 2024 and reported a record 444,000 total fraud cases in 2025. In July 2025 the UK Financial Conduct Authority issued fines related to weak onboarding and customer due diligence: £21 million to Monzo and £42 million across Barclays.
Standards and test results show limits of traditional liveness testing. ISO/IEC 30107‑3 provides a testing framework for presentation‑attack detection at the capture device but explicitly excludes software‑side injection attacks. NIST’s FATE PAD evaluation tested dozens of passive face PAD algorithms and found large performance differences across attack types and better results from fusion of multiple signals.
Regulators and standards bodies distinguish presentation attacks from injection attacks. Presentation attacks involve physical artifacts presented to a camera, such as printed photos, screen replays or masks. Injection attacks involve feeding pre‑rendered frames or synthetic streams into the verification pipeline via virtual cameras, emulators or intercepted SDK and API calls so no physical lens ever records the face. ENISA’s Remote ID Proofing Good Practices (2024) and NIST SP 800‑63‑4 (final, 2025) treat detection of presentation attacks and protections against injection attacks as separate controls.
Technical controls beyond the camera are cited in guidance and testing. Device and environment signals include virtual‑camera detection, emulator checks, operating system attestation, frame‑timing analysis and indicators of rooted or jailbroken devices. Document binding can use NFC chip reads and issuer signature verification to validate credentials independently of visual inspection. Verifier‑side signals such as transaction velocity, repeated‑pattern detection of synthetic identities and anomaly analysis on face vectors provide population‑level detection.
Standards and regulatory instruments offer alternative evidence rails. W3C Verifiable Credentials 2.0 (May 2025) and ISO/IEC 18013‑5 mobile driving‑licence specifications define issuer‑signed credentials and selective disclosure. NIST’s AI 100‑4 report and the UK NCSC recommend provenance and cryptographic authenticity as durable defenses. The EU AI Act (Article 50) requires labels for AI‑generated content but does not shift supervisory responsibility from verifiers. The EU Implementing Regulation on Digital Identity Wallets sets technical rules for issuer‑signed identity data and tightened remote onboarding requirements.
Procurement and supervision expectations now focus on evidence packages rather than single liveness metrics. Regulators expect institutions to retain PAD test results, IAD signals, device attestations, document chip reads, model versions and the logic behind automated decisions as part of a reviewable audit trail.